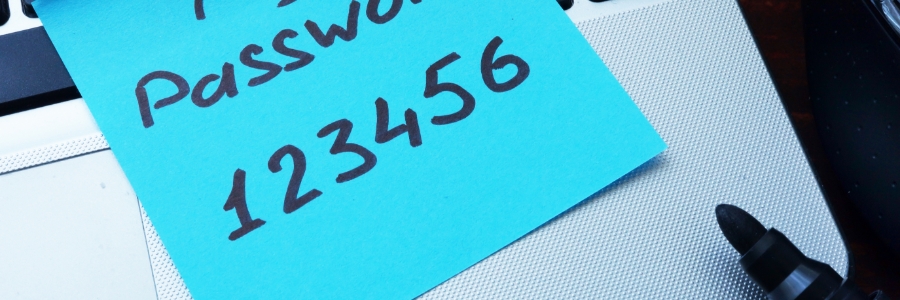
The influx of Gen Z talent into the workforce brings a wealth of digital expertise. However, their digital experience may include areas requiring additional security awareness. This blog will explore practical solutions to ensure smooth employee integration while maintaining a robust cybersecurity framework. With 2024 rolling on, the Gen Z workforce is poised to join… Continue reading A proactive approach to cybersecurity in the Gen Z workplace
A proactive approach to cybersecurity in the Gen Z workplace